Cybersecurity
Open Source Developer Tips
Lessons
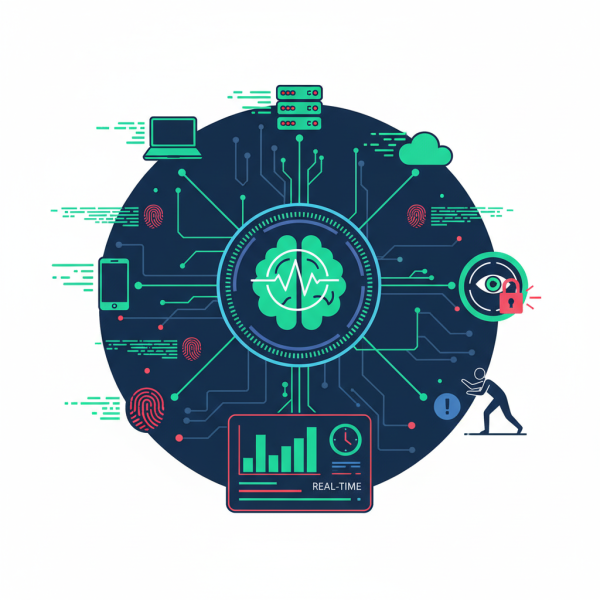
Real-time Monitoring and Logging for Threat Detection
Real-time monitoring and logging tools are crucial for cybersecurity, enabling proactive detection of suspicious activities and security events via comprehensive data analysis.
Enforcing Two-Factor Authentication Across All User Roles
Implementing and enforcing two-factor authentication (2FA) for all user roles is critical for preventing unauthorized access and bolstering an organization's digital defense.
WordPress Threat Motivations and Attack Vectors
This article dissects the WordPress cyber threat landscape, outlining common attack vectors like vulnerable plugins and diverse motivations from financial gain to hacktivism.
10 Essential Steps to WordPress Security
Mastering WordPress security is crucial for open-source users, involving robust updates, secure configurations, and proactive defense mechanisms to protect valuable digital assets from evolving cyber ...